Hydranet Monthly Recap #43 — February 2026
February continued with steady behind-the-scenes progress as the team remained focused on preparing Hydranet for the next stages toward mainnet. While public-facing releases have been limited, important work has been ongoing around the Lithium audit process and strengthening the security surrounding the Hydranet ecosystem.
Lithium audit progress
Work on addressing the findings from the Lithium audit is still ongoing. Fixing the reported issues is not simply a matter of adjusting the on-chain contract. Each change requires redeploying updated contracts and validating them across the broader infrastructure to ensure everything functions correctly together.
As anyone with development experience knows, making several changes at once can quickly turn into a time-consuming nightmare. A new deployment may introduce unexpected behavior elsewhere in the system, and tracking down the source of an issue when multiple updates have been introduced all at once can sometimes take hours of careful debugging.
For this reason, the remediation process is being handled deliberately and thoroughly. Each fix is implemented, redeployed, and tested within the wider infrastructure before moving forward. This approach does take time… But it ensures the final result is more stable, predictable, and ready for the next stage of verification.
Strengthening our ecosystem security
Another initiative this month involved working with an online security firm focused on protecting crypto projects from scams and impersonation attempts. These services specialize in identifying malicious content targeting a project, which includes phishing websites, fake social media profiles, impersonated team members, and fraudulent Telegram groups. Followingly, they coordinate takedowns with hosting providers and platforms.
During a short testing period, the firm identified 65 threats targeting the Hydranet brand across domains and social platforms. Many of these included fraudulent websites advertising fake HDN airdrops, impersonation accounts on social media, and Telegram channels attempting to mimic official community spaces. Even fake Medium articles promoting scam campaigns were detected.
Once identified, these threats are handled one by one through takedown requests to the service providers. Websites can often be removed relatively quickly, while social platforms, particularly Telegram groups, sometimes require more time to resolve.
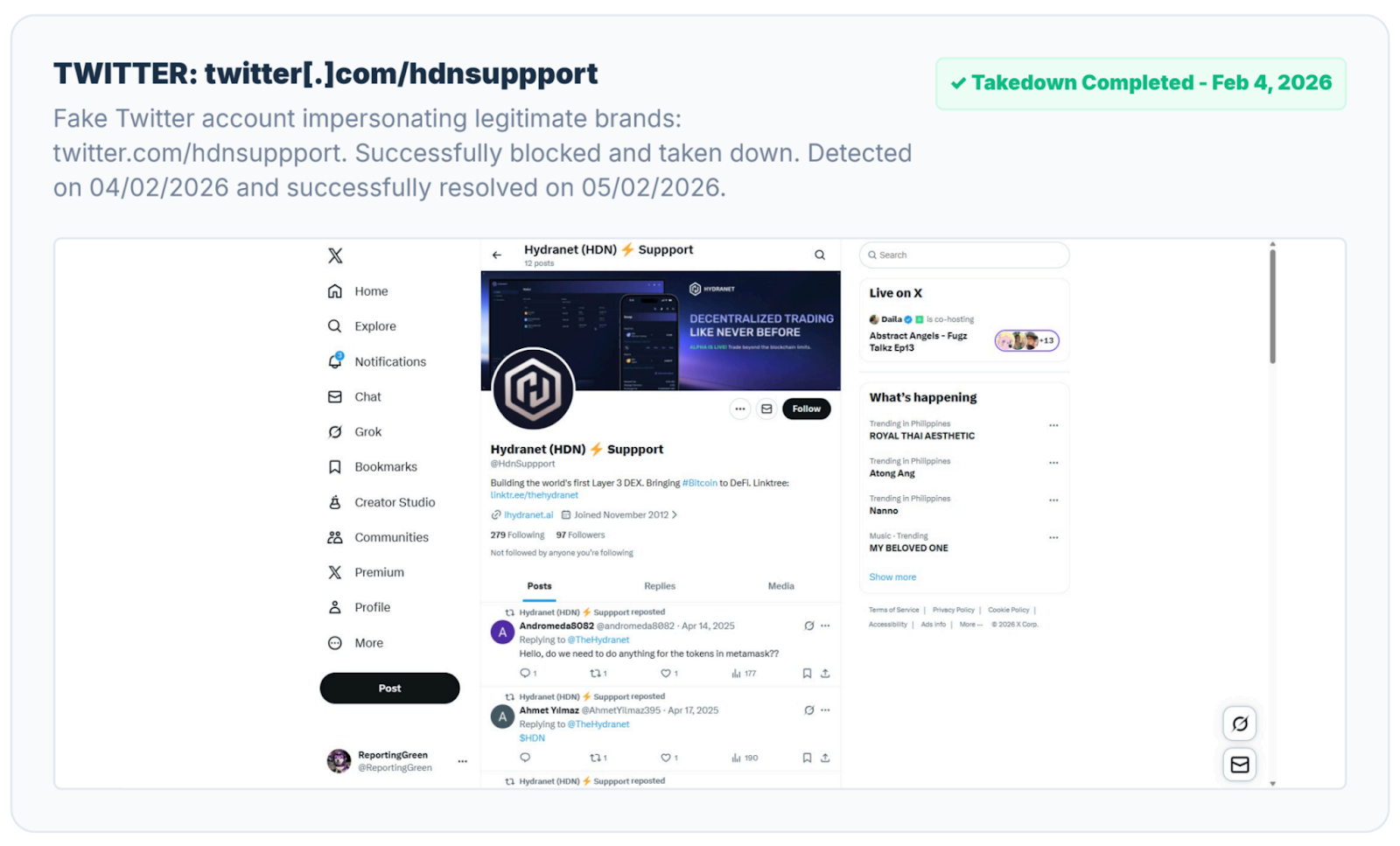
The results from this short testing period were impressive and provided valuable insight into the scale of scam activity surrounding crypto projects in general, and, more specifically, the extent to which such activity targets Hydranet.
While Hydranet has not yet reached mainnet, we decided to treat this engagement as a trial period and pause the service for now. However, we recognize that exposure, and with it the risk of impersonation and phishing attempts, tends to increase as projects grow. For that reason, we will remain in close contact with this security partner as Hydranet approaches later stages and broader public exposure.
As always, stay safe out there and remember:
- Hydranet team members will never ask for your seed phrase, passwords, or funds in exchange for support.
- If anyone claiming to represent Hydranet requests sensitive information or financial compensation, it is a scam.
- Always verify official channels and stay cautious when interacting with unsolicited messages.